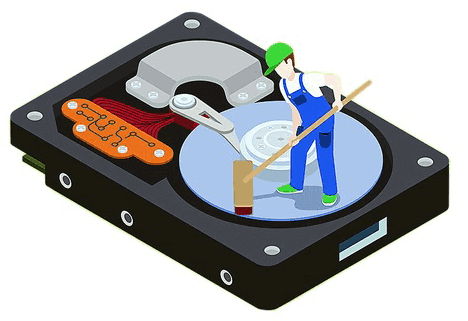
Understanding File Systems And Hard Disks
By BlackHammer / August 20, 2021
Understanding key terms of File systems and Hard Disks though are important for hackers. Before we want to learn real...
Read More
10 Replies

![[BEST] Whatsapp Vs Telegram Vs Signal: Which Is MoreSecure in 2020](https://www.thedarktech.com/wp-content/uploads/2019/12/Screenshot_20191206_211208.jpg)







![[New]PUBG Hack (No Root, No Ban) January 2021 | Including Paid Hacks Fully Antiban(Updated).](https://www.thedarktech.com/wp-content/uploads/2019/10/Pubg-hack.jpg)




![[BEST] Whatsapp Vs Telegram Vs Signal: Which Is MoreSecure in 2020](https://www.thedarktech.com/wp-content/uploads/2019/12/Screenshot_20191206_211208-375x200.jpg)


